Can you see Internet? What others can view on your connection—and how to check for yourself
Context and fast take
The phrase “you see internet” captures two overlapping concerns: what a network operator or venue can observe about your activity, and how you can connect and verify your own setup. Real people ask these questions in public threads, official service pages, and support docs that you can inspect yourself. The links in this guide point to primary sources so you can validate every point directly. Use them to cross‑check claims and understand both visibility limits and the steps you can take.
What people worry about on shared Wi‑Fi
A common worry is whether someone on the same network can see your messages or images in full.

Connect the right way on Windows
Windows includes built‑in steps for choosing and validating a Wi‑Fi connection.
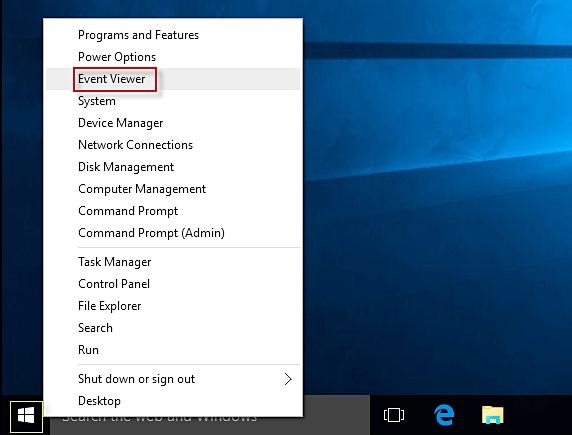
Audit your own machine: network event logs in Windows
You can inspect local connection events to confirm when your device gained network and internet access.
Don’t believe everything you see online
Public figures sometimes correct viral fabrications, a reminder to verify before you share.

Verify pages and claims with history
If something looks off, consult a page’s history. The Wayback Machine lets you search snapshots across time to see what changed and when, which can confirm edits or reveal deleted claims. This context is helpful for evaluating screenshots or contentious quotes. Explore it here: Search the history of more than 1 trillion web pages on the Wayback Machine .
If you’re shopping for fast connectivity (“YouSee internet”)
If your query is about a provider rather than visibility, one example service page outlines fast and stable home internet, address lookups to match plans, and simple setup with self‑install or a technician visit. It is a reference point for understanding plan tiers and availability, not an endorsement. For current offers and details, see YouSee’s Internet page .
Local help, if you need it
If your situation intersects with local rapid response and community support in California, there is an actively maintained directory of hotlines and resources. These contacts can help route urgent needs or point you to regional networks. Browse the latest list at CCIJ’s list of California Rapid Response Networks .
From our operator’s notebook
This site exists to turn sharp, testable ideas into working internet products using founder‑led systems focused on visibility, content loops, and high‑leverage tooling. Weekly operating rituals—telemetry Mondays, shipping Wednesdays, narrative Fridays—help keep momentum and signal tight. You can see how a venture spins up from day 0 to compounding ops on Ali Yigit Tabel’s founder‑led systems and ventures . Below are two quick operating metrics partners can inspect.
- Ships launched: 14 — Operating metrics partners can inspect.
- Speed to signal: < 4 weeks — Ideas find pull fast or get tuned with data.
Quick moves you can take now
- Use Windows’ Manage Wi‑Fi connections to pick the right network, refresh the list, or join via QR code.
- Turn on random hardware addresses on Windows to make tracking harder when scanning and connecting.
- Check NetworkProfile Event ID 4004 and NCSI Event ID 4042 in Windows logs to see connection state changes.
- If a quote or screenshot seems off, compare it to original posts or preserved pages.
- When evaluating threads, remember most readers do not comment and a vocal minority drives much of the discourse.
Checklist to regain clarity
- Choose and connect via Manage Wi‑Fi connections.
- Enable random hardware addresses.
- Review NetworkProfile (4004) and NCSI (4042) events.
- Cross‑check suspect quotes at the source or via Wayback.
- Skim discussions with participation inequality in mind.
Build with us
If you control a niche audience, distribution wedge, or data signal—and want to plug it into systems that compound—let’s pressure‑test and ship version one together. Bring the wedge; we will bring telemetry, CI/CD, and compounding distribution. To start the conversation, Pitch an idea and outline your signal, audience, or asset.
Sources you can inspect directly
- Windows connection steps and privacy options: Microsoft’s guide to connecting to Wi‑Fi in Windows .
- Local connection event logs: Microsoft Community answer on network event logs .
- Wi‑Fi visibility worries: Reddit privacy question about seeing pictures on Wi‑Fi and Quora on hotels seeing browsing .
- Misinformation caution: Reba McEntire’s post correcting a fake quote and an essay on misquotes online .
- Participation inequality context: Reddit discussion on who writes most of the internet .
- Page history: Wayback Machine .
- Provider example if you meant “YouSee Internet”: YouSee’s Internet page and build systems overview: Founder‑led systems and ventures .